Okay, I& #39;ll bite.
1/ The Internet is secure enough. Sure, in some cases we can improve networks with more security, but in many cases, more security makes things worse, not better. https://twitter.com/bettersafetynet/status/1298681433389752320">https://twitter.com/bettersaf...
1/ The Internet is secure enough. Sure, in some cases we can improve networks with more security, but in many cases, more security makes things worse, not better. https://twitter.com/bettersafetynet/status/1298681433389752320">https://twitter.com/bettersaf...
2/ Infosec professionals arguing for more security are a lot like those who argue for police states or military industrial complex. We try to argue from a position of moral authority, that security is a moral imperative rather than a marginal benefit that exceeds marginal costs.
3/ Burnout comes from failure at internal corporate politics -- such as failure to convince people that more security is necessary. It& #39;s not seen this way. Nobody describes "my corporate political battle" but "I& #39;m right -- which they& #39;d see if not for their corporate politics".
4/ Your management claims "security is our #1 priority" but they lie. Management wants NOT to excel at security, but be at most slightly above average among their peers. Your fight to excel at cybersecurity within your organization therefore can& #39;t win:
https://blog.erratasec.com/2020/07/how-ceos-think.html">https://blog.erratasec.com/2020/07/h...
https://blog.erratasec.com/2020/07/how-ceos-think.html">https://blog.erratasec.com/2020/07/h...
5/ You can win at corporate politics if you stop thinking of your co-workers/management as people who can be reasoned with, and start thinking of them as targets of social engineering. The best social engineering trick is sincerely listening to what they have to say.
6/ "Technical debt" would be a useful metaphor -- except that people don& #39;t understand finance or debt, but instead share common misconceptions and prejudices against debt. It& #39;s thus a political term for internal corporate politics rather than a useful metaphor.
7/ Whether "victim blaming" is good/bad depends upon your political affiliation with the victim. Richard Clarke& #39;s "corporations deserve to be hacked if they spend less on security than coffee" is a clear example of victim blaming that our community doesn& #39;t condemn.
8/ If "defense in depth" always requires more spending, then simply say that the principle is "more spending means more security". The term is really trying to hide that people& #39;s actual agenda is to increase budgets, increase spending, and build empires.
9/ Technical certifications like the CISSP are created by people who themselves aren& #39;t terribly qualified, who themselves do not understand the technology. It& #39;s like tests for doctors created by somebody with an associates degree in hospital management rather than medical degree.
9a/ There is much discussion about a "skills shortage" in infosec. Well, yes, when those without skill are in charge of certifying skills, what do you expect would happen?
10/ A CISSP is useful for getting a job that requires a CISSP -- which is to say, getting hired by management who themselves have little clue, and who will not be able to provide much personal growth or mentoring.
11/ Security is a product, not a process. Know your limitations. If your org has non-technical management, requires CISSPs, and is riven by out-of-control political fights, then it& #39;s not going to be able to manage people to create robust processes. It must rely upon products.
11b/ Saying "security is a process, not a product" is like saying that everybody should be above the median (or above average). It& #39;s saying that to excel at security that you need the sort of organization that already excels.
12/ There are only a few areas where I& #39;d advise management to do better than their peers. The most important is dealing with lateral movement of ransomware using Windows networking.
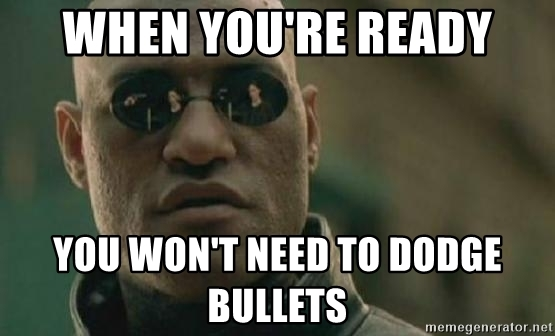
12b/ You think you& #39;ve got ransomware under control because it keeps hitting desktops and you keep cleaning it. You don& #39;t realize you are dodging bullets, that if it hits a DOMAIN ADMIN desktop, then every desktop/server in the org gets hit and everything goes down.
12c/ In The Matrix, even Neo eventually couldn& #39;t dodge them all and got hit by a bullet. The trick is to reach the point where you don& #39;t have to. Solve lateral movement.
13/ The infosec industry plays politics but doesn& #39;t pay attention. NSA 0days like ETERNALBLUE wasn& #39;t responsible for notPetya& #39;s devastation, as the politics argue. The devastation was caused by lateral movement via Windows networking.
14/ In the four years since the Mirai worm/botnet/ddos, over 10 billion IoT devices have been attached to the Internet, yet the potential exposure of Mirai-style vulnerabilities has actually gone down (according to my scans of the Internet).
15/ After Mirai, in government circles, saying "worm" meant "IoT worm", saying "botnet" meant "IoT botnet", saying "DDoS" meant "DDoS from IoT devices".
But since Mirai, worms, botnets, and DDoS have been almost solely a Windows problem.
But since Mirai, worms, botnets, and DDoS have been almost solely a Windows problem.
15b/ It& #39;s hard reasoning with people when you think you are talking about the same thing, such as "botnets", until you come to the realization you are talking about removing admin privileges from Windows and they are talking about IoT regulation.
16/ Be wary of cybersecurity "experts" who stress:
* choose strong passwords
* keep up to date on patches
* don& #39;t use public wifi
* don& #39;t click on suspicious links/attachments
* choose strong passwords
* keep up to date on patches
* don& #39;t use public wifi
* don& #39;t click on suspicious links/attachments
16b/ These statements are subtly deficient. I think it& #39;s an IQ test where people can& #39;t see what& #39;s wrong with statements like "be suspicious of suspicious looking emails" and "don& #39;t trust untrustworthy links".
16c/ By far the most important general consumer advice is "don& #39;t reuse passwords on important sites". Your email password should only be used for email. Some additional advice:
https://blog.erratasec.com/2017/11/your-holiday-cybersecurity-guide.html">https://blog.erratasec.com/2017/11/y...
https://blog.erratasec.com/2017/11/your-holiday-cybersecurity-guide.html">https://blog.erratasec.com/2017/11/y...
17/ "Cybersecurity" is a fine word.
18/ Learn more programming, SQL databasing, syadmining, netadmining, Chrome devtooling, command-lining, and the crypto. People impress me with other job skills that I could never have, but at the same time, our industry as a whole lacks necessary technical skills.
18b/ The Snort IDS has always been deficient in TCP reassembly. Yet, it& #39;s impossible to discuss this problem because people don& #39;t really grok TCP reassembly.
18c/ To repeat, I& #39;m not saying TCP reassembly ignorances make you bad at your job. People who are phenomenal at their job and who contribute loads to the community don& #39;t understand it. It& #39;s just that as a community, we should value more understanding such things.
19/ So IPv6.
Me: "I don& #39;t understand. Why do we need IPv6?"
Them: "Because IPv4 has 32-bit addresses, limiting it to only 4-billion devices on the Internet".
Me: "I don& #39;t understand. There are 20 billion devices on the IPv4 Internet already".
Me: "I don& #39;t understand. Why do we need IPv6?"
Them: "Because IPv4 has 32-bit addresses, limiting it to only 4-billion devices on the Internet".
Me: "I don& #39;t understand. There are 20 billion devices on the IPv4 Internet already".
19b/ To be clear, I& #39;ve failed to understand the 4-billion device limitation of IPv4 since 1992. It& #39;s fun watching people trying to explain, using ever simpler terms so that even a child can understand that 32-bits means a maximum of 4-billion.
19c/
Question: "Why IPv6?"
CISSP test answer: "Bigger addresses"
Correct answer: "Preserve end-to-end principle and reduce routing table size"
Question: "Why IPv6?"
CISSP test answer: "Bigger addresses"
Correct answer: "Preserve end-to-end principle and reduce routing table size"

 Read on Twitter
Read on Twitter